UGREEN 2 Pack USB C to USB C Charger Cable 100W Power Delivery
€12,89

UGREEN Right Angle USB C Cable 3.0 Type C Charger 5Gbps
€8,79
€10,99

UGREEN USB C to USB C Cable 60W
€6,99
€11,99

UGREEN USB C 90 Degree Cable 3A Right Angle Type C Charger Cable
€6,79
€9,49
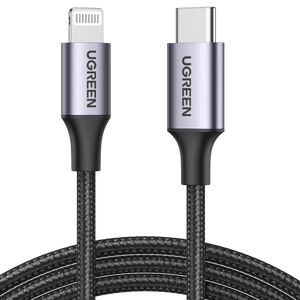
UGREEN USB C to Lightning Cable
€15,19
€18,99
Reflect 4 Proxy May 2026
Imagine a situation where you're using a proxy server (let's call it "Proxy 4") to access the internet. This proxy server could be configured in such a way that it reflects or redirects your requests in a manner that's useful for specific applications or security setups.